Secure Deliveries with
Verified and Trustworthy Drivers
Ensure compliance, prevent misconduct, and simplify document management.
Benefits
Why DriverTrust is for you?
More Security
Work with honest drivers to reduce theft, liability payments & insurance premiums
Honest drivers mean safer deliveries. At DriverTrust, we help you build a team of verified, trustworthy drivers, reducing the risks of theft, fraud, and operational mishaps. Here’s how DriverTrust enhances security for your business:
-
Fraud Prevention:
Our advanced verification tools ensure that every driver on your team has been thoroughly vetted, minimizing the risk of identity fraud or impersonation. By flagging individuals with a history of misbehavior, we help you prevent bad actors from joining your workforce. -
Theft Reduction:
With access to a shared database of driver misconduct across companies, you gain valuable insights into the reliability of potential hires. This proactive approach significantly reduces the likelihood of theft, ensuring your cargo reaches its destination safely. -
Lower Liability Payments:
Unverified drivers can lead to costly errors, including cargo theft, accidents, and delivery disputes. By working with honest and verified drivers, you mitigate these risks and avoid unnecessary legal and financial liabilities. -
Stronger Customer Relationships:
Security isn’t just about protecting assets; it’s about maintaining trust. Reliable deliveries by honest drivers lead to satisfied customers who are more likely to stay loyal to your business.
DriverTrust empowers your business to take control of driver security, ensuring every delivery is handled with care and integrity. By prioritizing transparency and accountability, you not only secure your operations but also set a new standard for professionalism in your industry.
Improved Conduct
Safeguard against crime & misconduct with enabled preventive & acute measures
Preventing issues before they happen. DriverTrust equips your business with the tools to ensure better driver conduct, minimizing risks and protecting your operations. Here’s how we help you stay ahead of potential challenges:
-
Proactive Crime Prevention:
With DriverTrust, you can identify and avoid hiring drivers with a history of misconduct. Our cross-company evaluation system provides insights into past behaviors, helping you build a team of reliable professionals. -
Real-Time Incident Management:
Our platform enables swift action against acute issues like theft, fraud and house and yeard bans. By maintaining up-to-date driver records and traffic light statuses, you can quickly address and resolve incidents as they arise. -
Enhanced Accountability:
DriverTrust fosters a culture of accountability by ensuring that drivers know their performance is tracked and evaluated. This transparency motivates better behavior and reduces the likelihood of misconduct. Honest drivers receive a “green status” within the system, visibly showcasing their reliability. This positive signal underscores their responsible behavior and grants them greater recognition across the network -
Operational Integrity:
Preventing misconduct is crucial to protecting your company’s reputation and operational efficiency. With DriverTrust, you safeguard your business against disruptions caused by significant unprofessional behavior. -
Peace of Mind:
Knowing that your drivers are vetted, monitored, and held to high standards lets you focus on growing your business instead of managing preventable crises.
DriverTrust doesn’t just manage driver conduct; it transforms it. By combining preventive measures with tools to address acute challenges, we ensure your operations run smoothly and securely.
Streamlining Operations
Automated Driver Reminders, Document Management, and Verification
Automation that works for you. DriverTrust takes the complexity out of managing drivers by automating key processes like reminders, document management, and verification. Here’s how we streamline your operations:
-
Automated Driver Reminders:
Never worry about missed deadlines or renewals again. DriverTrust sends automatic reminders for critical tasks such as license renewals and document uploads ensuring your drivers stay on track. -
Effortless Document Management:
Our platform streamlines the entire document workflow by guiding drivers to upload the specific files your business requires. Instead of storing documents, we focus on analyzing them and delivering a clear “traffic light” status for easy oversight. This ensures you gain quick access to essential compliance insights without hunting down paperwork or dealing with missing information. -
Seamless Driver Verification:
DriverTrust’s advanced verification tools eliminate the need for manual checks. Verify driver identities and credentials quickly and reliably, reducing the time spent on onboarding while ensuring compliance with the highest industry standards. -
Reduced Administrative Burden:
By automating routine tasks, DriverTrust allows your team to focus on higher-value activities instead of being bogged down by repetitive administrative work. -
Improved Operational Efficiency:
Streamlined processes mean fewer delays, better resource allocation, and smoother day-to-day operations—saving you time and money while ensuring consistency across your workforce.
With DriverTrust, managing drivers becomes simple, efficient, and reliable. Our automated solutions free you from operational bottlenecks, allowing you to focus on growing your business.
Avoid Compliance Risk
Secure document verification, and minize data retention risks and ensure adherence to regulatory storage limits
Compliance made simple. DriverTrust ensures your business stays ahead of regulatory challenges by securely managing documents, minimizing risks, and adhering to data retention requirements. Here’s how we help:
-
Secure Document Verification:
DriverTrust provides a robust system to verify driver documentation, ensuring compliance with industry standards and GDPR. Our platform reduces errors and maintains an auditable trail of compliance for inspections or audits. -
Minimized Data Retention Risks:
Avoid unnecessary liabilities by ensuring that sensitive data is stored only for the required duration. DriverTrust automatically flags and manages outdated records, protecting your business from non-compliance penalties. -
Adherence to Storage Limits:
Regulatory storage limits can be complex to navigate. DriverTrust helps you stay compliant by tracking document lifecycles and securely disposing of expired records, eliminating the risk of retaining unnecessary data. -
Reduced Legal Exposure:
Failing to comply with document verification and retention regulations can result in heavy fines and reputational damage. DriverTrust’s secure, automated system ensures your business is always in line with legal requirements. Drivers can be sure that their documents are stored in compliance with GDPR. -
Simplified Compliance Management:
With all compliance-related tasks centralized on one platform, DriverTrust makes it easy to manage driver documents, monitor updates, and demonstrate adherence to regulations.
DriverTrust provides peace of mind by minimizing compliance risks and securing your data. By automating these processes, we enable you to focus on your operations without worrying about regulatory hurdles.
How It Works
Setup your organisation and invite drivers in less than 30min.
In just 5 steps, you can start using our all-in-one platform for document verification, cross-company evaluation, and task automation.
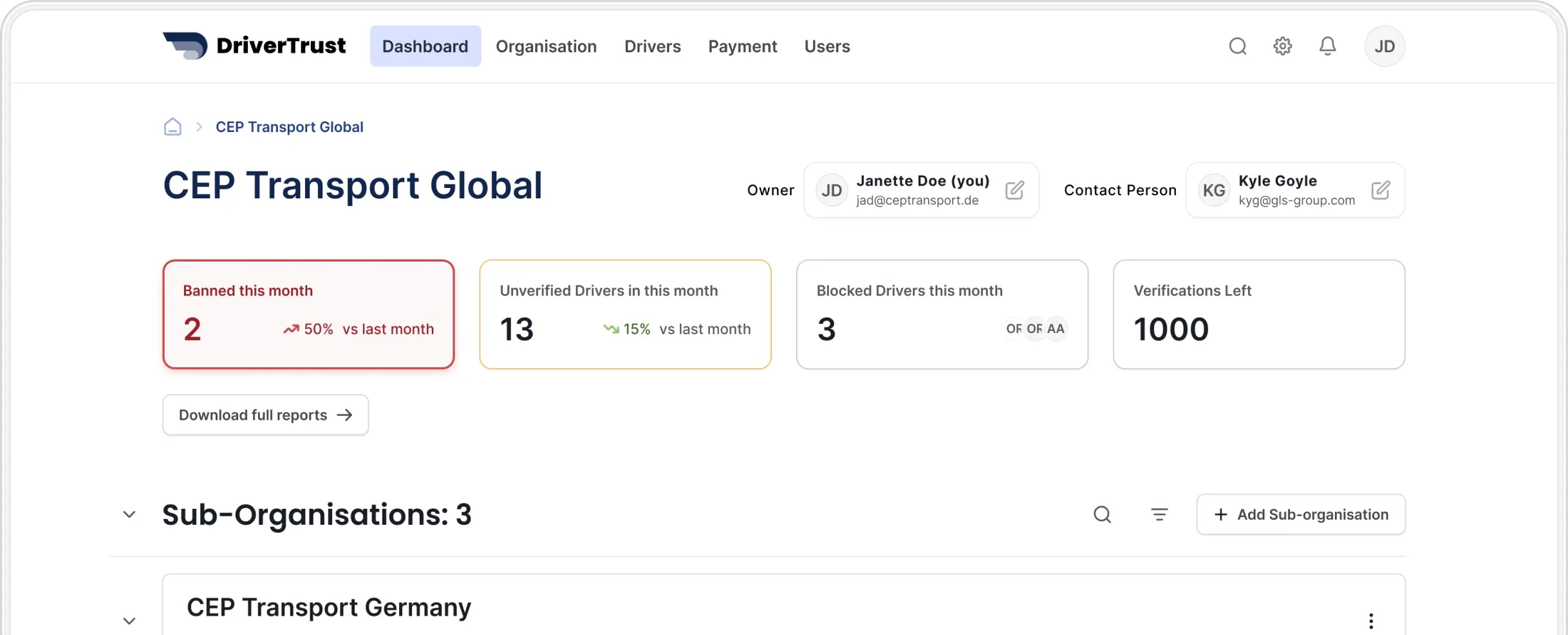
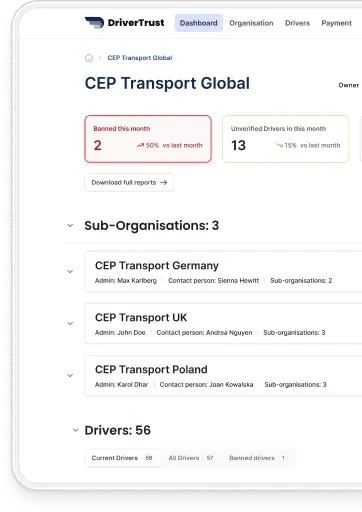
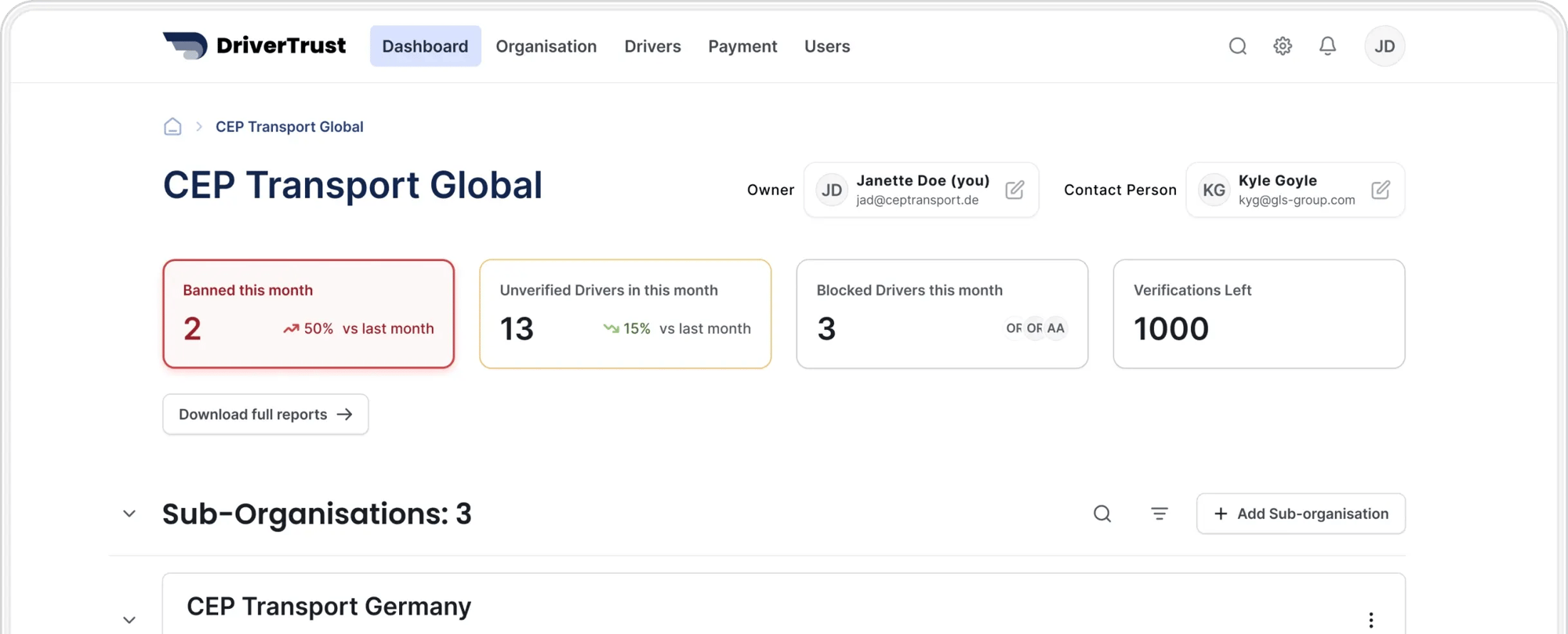
Step 1: Setup your organisation
Create an account and quickly create a profile for your company.
Step 2: Invite Drivers
Inviting drivers to DriverTrust sends them an invitation to create account in the mobile app available in the official app stores (Google, iOS)
Step 3: Driver verifies their documents through the mobile app.
Drivers upload their legal documents (e.g., ID, driver’s license, work permit) through our user-friendly interface, available in multiple languages.
Our system automatically verifies the validity of the uploaded documents and checks for any discrepancies or expired credentials.
Step 4: Drivers gets statuses
Based on document verification and weighted factors (e.g., theft incidents, training completion), drivers receive a traffic light status.
If a driver has worked for other companies in the past, and they got a “House and Yard” ban, it will be visible to you.
Step 5: You are all set!
Our platform sends automated reminders to drivers when documents are about to expire, ensuring they remain compliant. Companies receive real-time alerts if a driver’s status changes.
Step 1: Setup your organisation
Create an account and quickly create a profile for your company.
Step 2: Invite Drivers
Inviting drivers to DriverTrust sends them an invitation to create account in the mobile app available in the official app stores (Google, iOS)
Step 3: Driver verifies their documents through the mobile app.
Drivers upload their legal documents (e.g., ID, driver’s license, work permit) through our user-friendly interface, available in multiple languages.
Our system automatically verifies the validity of the uploaded documents and checks for any discrepancies or expired credentials.
Step 4: Drivers gets statuses
Based on document verification and weighted factors (e.g., theft incidents, training completion), drivers receive a traffic light status.
If a driver has worked for other companies in the past, and they got a “House and Yard” ban, it will be visible to you.
Step 5: You are all set!
Our platform sends automated reminders to drivers when documents are about to expire, ensuring they remain compliant. Companies receive real-time alerts if a driver’s status changes.
Features
Driver Verification & Compliance
Automated Document Upload & Review
Drivers upload their IDs, licenses, and permits and they are are automatically verified.
Real-Time Status Updates
Instantly see whether your drivers are compliant with legal requirements.
Cross-Company Evaluation
See if drivers have had issues with previous employers or received bans from other companies.
Pricing
Compare our plans and find yours
Simple, transparent pricing that grows with you.
Starter
Plus
popularEnterprise
Enterprise
€2,20
per driver / mo. No drivers min.€1,90
per driver / mo. 500 drivers min.Custom
1000 drivers min.Custom
750+ annual min. verificationOptimization of personnel
screening (even before hiring)
Identify and onboard the most reliable drivers by screening their profiles thoroughly, even before hiring. Our platform helps ensure you select the best candidates for your team.
Cross-company consideration of
House & Yard bans
Access shared data on house and yard bans across companies which is reflected in red light statuses to prevent hiring individuals with a history of misconduct or violations.
Prevention of identity fraud
Leverage our advanced identity verification platform to ensure driver authenticity and minimize the risk of fraud or impersonation. Our process begins with AI-driven analysis of uploaded documents; if these are unreadable or inconclusive, a human reviewer steps in. We aggregate risk levels based on a wide range of factors—cross-referencing data against blacklists and industry sources, examining device attributes like IP addresses and background audio cues, and generating privacy-compliant, non-reversible biometric encodings from facial images. If the combined risk surpasses predefined thresholds, a dedicated fraud specialist is engaged for further verification. This holistic, GDPR-compliant approach ensures reliable identity checks without compromising user privacy.
Automated reminders to the drivers
Set automated reminders for drivers to complete critical tasks such as document renewals or compliance updates, ensuring smooth operations.
Legal protection of the
examination of the documents
Stay compliant with legal requirements while verifying driver documents, protecting your business from regulatory risks.
Risk reduction GDPR Retention of
personal data
Minimize GDPR-related risks by securely managing and retaining driver data only for the required duration.
Real-time notifications when
the driver status changes
Receive instant updates whenever a driver’s status changes, helping you act quickly on critical information.
Driver status change history
Access a detailed history of all driver status changes for transparency and better decision-making.
API Interface
Integrate DriverTrust seamlessly into your existing systems using our flexible API interface. All functionalities and results can be displayed and managed your own system.
Automated blocking for the
negative statuses
Automatically block drivers with negative statuses to prevent operational risks and ensure safety.
Starter
€2,20
per driver / mo. No drivers min.Optimization of personnel
screening (even before hiring)
Cross-company consideration of
House & Yard bans
Prevention of identity fraud
Automated reminders to the drivers
Legal protection of the
examination of the documents
Risk reduction GDPR Retention of
personal data
Plus
popular€1,90
per driver / mo. 500 drivers min. Everything from Starter, plus:Real-time notifications when
the driver status changes
Driver status change history
Enterprise
Custom
1000 drivers min. Everything from Plus, plus:API Interface
Automated blocking for the
negative statuses
Enterprise
Custom
750+ annual min. verification Everything from Enterprise, plus:All prices excl. a one-time setup fee of €2,20 per driver and VAT.
Whitepaper
The Urgent Need to Address Cargo Crime
Cargo theft causes an estimated €8.2 billion in annual damage across the EU - and the threat is escalating fast: reported cargo theft in Europe increased by 438% in one year.
Behind this surge is a new generation of cargo crime. Criminal networks increasingly use fake carriers, insider knowledge, identity fraud, multiple identities and Fraudulently Obtained Genuine Documents (FOGD) to exploit legitimate logistics processes. FOGD creates a critical security gap: identity documents can be officially issued, technically genuine and still be based on a fraudulent identity. 
The whitepaper explains:
- why cargo theft is increasingly driven by fake carriers, insiders and strategic deception
- why FOGD is especially difficult for traditional document checks to detect
- why biometric 1:1 verification does not reliably prevent multiple identities
- why continuous 1:n matching is critical for modern driver identity verification
- which transparency gaps arise from criminal record checks and subcontractor structures
- why manual document processes create compliance and data protection risks
- what capabilities a modern solution for logistics fraud detection and compliance needs
Whitepaper
News
Upcoming new features
Additional Documents
Make your own documents a requirement for your drivers.
Reporting
Get a centralized report of all of your drivers and their current statuses.
Ensure Compliance with Custom Requirements
The DriverTrust Additional Documents feature allows you to set tailored document requirements for your drivers. Whether it’s company-specific regulations, working permits, or other critical documentation, you can seamlessly collect and manage these files to maintain compliance and operational standards.
- Customizable Requirements: Request specific documents that align with your company’s needs and policies.
- Simplified Compliance: Ensure all drivers meet working permit and regulatory standards effortlessly.
- Centralized Management: Collect, verify, and store documents securely within one unified platform.
Keep your business compliant and organized with streamlined document workflows designed for flexibility and control.
Centralized Insights for Driver Performance
DriverTrust’s Reporting feature gives you a centralized report of all your drivers and their current statuses, empowering you to make informed decisions with ease.
- Driver Status Overview: View a comprehensive, up-to-date summary of your entire fleet’s activity, identity validations, and compliance status.
- Performance Insights: Identify top-performing and reliable drivers while pinpointing areas of concern, such as compliance gaps or risks.
- Actionable Data: Access detailed analytics to reduce theft risks, liability payments, and operational inefficiencies.
With Reporting, you have the clarity and control to optimize your fleet’s performance, reduce risks, and enhance security.
Special Promotion
Early Bird offer
Secure exclusive savings when you pay upfront for 12 months
and scale your operations efficiently.
- No Setup Fee. Save €2,20 per driver
- Save up to 25% monthly with the exclusive Early Bird rates compared to standard pricing
- Secure overall savings for each active driver per year:
- €4,84 (Starter) | - €6,76 (Plus 100) | - €7,84 (Plus 500)
If you have any questions regarding the special offer,
we are always ready to answer them.
FAQs
Everything you need to know about the product and billing. Can’t find the answer you’re looking for? Please chat to our friendly team.
What is DriverTrust?
DriverTrust is an advanced yet user-friendly solution designed to enhance asset security and streamline efficiency in delivery and logistics operations. It features an intuitive driver app for effortless driver verification, paired with a straightforward web portal that simplifies cross-company evaluations and automates tasks, ensuring seamless monitoring and management of operations.
Does DriverTrust integrate with existing company systems?
Yes, DriverTrust is designed to integrate seamlessly with existing company systems. By leveraging modern APIs and flexible architecture, DriverTrust can connect to your current tools and platforms, ensuring smooth data flow and minimal disruption to your operations.
How does DriverTrust help reduce operational costs?
By preventing theft, DriverTrust reduces losses and associated costs. Additionally, its streamlined and automated processes save time, leading to increased efficiency and cost savings.
How does DriverTrust help reduce fraud?
By performing thorough identity verification, maintaining a cross-company driver status database, and minimizing risks associated with falsified driver credentials.
Is the DriverTrust app compatible with older smartphones?
Yes, DriverTrust is designed to work on a wide range of smartphones, including older models, making it accessible for all drivers.
How does cross-company driver evaluation work?
DriverTrust uses a traffic light system for cross company evaluation. The traffic light status is generated based on different weighted factors such as Fraud detection, Document validity, House & Yard Ban, Blacklist Checks and Upload time adherence. The data is gathered from the DriverTrust web platform and entered house & yard bans as well as the DriverTrust App which uses thorough fraud prevention with hundreds of checks performed in a few seconds in a simple workflow that is partly based on the leading verification services, blacklists, industry cross-links, risk levels, fraud agent interference, and biometric encodings to ensure GDPR compliance.
Can drivers see their own traffic light status?
Yes. The DriverTrust app gives drivers direct access to their traffic light status and verification status.
Can drivers dispute traffic light statuses?
The platform includes a transparent dispute resolution mechanism for drivers. If you wish to learn more about this, please feel free to contact us.
How does DriverTrust comply with data privacy regulations?
DriverTrust has advanced data protection technology in place that ensures data security and GDPR compliance, besides its contractual setup. Data exchange and storage are based on different contracts that are established when using the solution between the involved parties. If you wish to learn more about this, please feel free to contact us.
What does FOGD mean?
FOGD means Fraudulently Obtained Genuine Documents. The term refers to genuine, officially issued documents that were obtained on a fraudulent basis. Such documents may be technically genuine, contain authentic security features and still be based on a false or manipulated identity foundation. Interpol expressly distinguishes, in the area of identity and travel document fraud, between false documents and genuine documents that are misused or obtained fraudulently. FOGD is therefore not limited to one specific industry. It is relevant wherever identity determines access, trust, eligibility or authorization. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Why are fraudulently obtained genuine documents more dangerous than classic forged documents?
Fraudulently obtained genuine documents are particularly dangerous because the document itself can be formally genuine. In classic forgery cases, the defect is often visible in the document itself, for example in a counterfeit passport, an altered data page or a non recognized pseudo document. In FOGD cases, the problem usually lies earlier in the issuance process. A public authority may have issued a genuine document, but on the basis of manipulated identity evidence, false source data or other deceptive input. This is precisely why FOGD can pass even high quality document checks. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
What is the difference between FOGD and forged documents?
Forged documents are not genuine, have been altered or are not officially recognized. FOGD, by contrast, refers to genuine documents that were obtained through deception. The fraud does not necessarily lie in the document itself. It lies in the fact that the genuine document was issued on the basis of a fraudulent identity foundation. Interpol lists relevant categories including counterfeits, forgeries, pseudo documents, the misuse of genuine documents by impostors and fraudulently obtained genuine documents. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Why can a normal document check fail to reliably detect FOGD?
A normal document check mainly verifies whether a document appears genuine, whether security features are present and whether the presenting person matches the document. In a FOGD case, all of this may be true. The document may be genuine, the chip may be genuine, the security features may be genuine and the biometric comparison may return a positive result. Nevertheless, the underlying identity may have been established on a fraudulent basis. ICAO points out that the processes used to establish and verify a person’s identity can often be weaker than the security of the document issued later. (https://www.icao.int/sites/default/files/TRIP/Publications/ICAO-Guide-on-Evidence-of-Identity.pdf)
In which areas can FOGD create security risks?
FOGD can create security risks wherever a genuine document creates trust. This includes, for example, logistics, transport, staffing, platform work, financial services, telecommunications, insurance, building security, access to critical infrastructure, healthcare, public authority processes, online accounts, payment processes and any form of Know Your Customer or Know Your Worker verification. Logistics is one particularly clear example because drivers, service providers, contractors and external personnel may gain access to goods, sites and sensitive process information. However, the underlying problem is cross sectoral: fraudulently obtained genuine documents can make a false or manipulated identity appear legitimate. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
What do Fraudulently Obtained Genuine Documents have to do with corporate security risks?
FOGD is relevant for companies because criminal actors do not only attack from the outside. They may also present themselves as legitimate employees, service providers, contractors, customers, drivers, platform users or authorized personnel. If a person presents a genuine document that was obtained fraudulently, that person may gain access to goods, buildings, data, systems, payments, confidential information or security critical processes. FOGD therefore creates risks for insider crime, identity fraud, multiple identities, social engineering and trust based access processes. (https://www.cisa.gov/topics/physical-security/insider-threat-mitigation)
Why is protection against FOGD important in access critical industries?
Protection against FOGD is important because in many industries a person’s identity determines operational privileges. People may gain access to buildings, goods, IT systems, customer data, financial processes, sensitive information or security critical work areas. If a fraudulently obtained genuine document is accepted without detecting the underlying identity risk, a person may appear formally legitimate even though the identity foundation is false or manipulated. This creates a security gap between document authenticity and actual trustworthiness. CISA describes insider risks generally as threats involving persons who have authorized access to, or knowledge of, an organization’s resources. (https://www.cisa.gov/topics/physical-security/insider-threat-mitigation)
Why is logistics a useful example of FOGD risks?
Logistics shows very clearly why FOGD is practically relevant, but it is only one example. Drivers, contractors, service providers and external personnel may assume operational key roles, collect goods, enter sites, view shipment data or trigger security processes. In Fake Carrier scenarios, criminal actors may also exploit apparently legitimate identities, documents or company related structures to obtain access to shipments or transport processes. If a fraudulently obtained genuine document is used in such an environment, it can create a false sense of security: the document appears genuine, the person appears authorized and the identity risk remains hidden. Comparable risks exist wherever internal or external persons gain access to sensitive resources. (https://www.cisa.gov/topics/information-communications-technology-supply-chain-security)
Why is a biometric 1:1 check not sufficient to protect against FOGD?
A biometric 1:1 check verifies whether a person matches one specific document or one specific data record. It does not automatically verify whether the same natural person has already been registered under a different identity. This is critical in FOGD cases because the person may match the fraudulently obtained genuine document, while still using a manipulated identity foundation. NIST describes biometric verification as a 1:1 comparison and distinguishes it from 1:n identification or deduplication against a larger data set. (https://pages.nist.gov/800-63-4/sp800-63a/ial/)
Why does protection against FOGD require a 1:n comparison?
Protection against FOGD requires more than the verification of one isolated identity. The decisive question is whether the same natural person has already appeared under different identity data, with different documents or in another organizational context. Only a continuous 1:n comparison can make multiple identities, repeated registration attempts and identity changes visible. The World Bank describes deduplication as a central mechanism for detecting multiple registrations in identity systems. (https://id4d.worldbank.org/guide/biometric-data)
What is the relationship between FOGD and multiple identities?
FOGD and multiple identities are closely connected. A person may use genuine documents obtained fraudulently to build several formally plausible identities. Each individual identity may appear unremarkable when checked in isolation. The actual risk arises when the same natural person appears multiple times in a system or network and is still not recognized as the same person. Interpol describes identity and document fraud as a phenomenon in which both false and genuine documents can be used fraudulently. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Why are fraudulently obtained genuine documents harder to detect than stolen documents?
Stolen documents can sometimes be identified through loss reports, watchlists or databases. In FOGD cases, by contrast, there is often no stolen document. The document was issued by a genuine authority and is formally valid. Therefore, FOGD cannot be detected merely by asking whether a document is genuine, stolen or expired. The relevant risk lies in how the document was obtained and whether the identity behind it is reliable. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
What role do breeder documents play in FOGD?
Breeder documents are source documents used to establish or support an identity, such as birth certificates or evidence of origin. If such source documents are forged or manipulated, they can later be used to obtain a genuine identity document. This creates a FOGD risk because the later document may be technically genuine even though the identity foundation is false. ICAO points out that the processes used to establish and verify identity can often be weaker than the security of the document issued later. (https://www.icao.int/sites/default/files/TRIP/Publications/ICAO-Guide-on-Evidence-of-Identity.pdf)
Why does a secure passport alone not protect against FOGD?
A secure passport protects against many forms of classic document forgery. However, it does not fully protect against the possibility that the passport was issued on the basis of false identity information. With FOGD, the problem is not the passport as a technical document. The problem is the identity that led to its issuance. FOGD must therefore be understood as an identity and issuance problem, not only as a document problem. ICAO expressly describes the need to reliably establish the applicant’s identity in the secure issuance of travel documents. (https://www.icao.int/sites/default/files/TRIP/Publications/Guide-PART-1-Format-Revised-27March.SM.pdf)
Why is protection against FOGD particularly relevant for service providers, contractors and external personnel?
Protection against FOGD is particularly relevant when external persons gain access to internal processes, customer data, goods, buildings, systems or confidential information. Modern value chains often rely on service providers, contractors, subcontractors and changing external personnel. If such a person presents a genuine document obtained fraudulently, that person may appear trustworthy even though the underlying identity is not reliable. CISA describes modern organizational environments as networks of third party vendors, suppliers, service providers and contractors, which increases the importance of robust identity and access controls. (https://www.cisa.gov/topics/information-communications-technology-supply-chain-security)
Why is corporate screening not sufficient to protect against FOGD?
Corporate screening mainly checks companies, licenses, register data, insurance coverage, certificates or commercial plausibility. FOGD, however, concerns the natural person who actually gains access to resources, processes or sensitive information. A company may appear formally unremarkable while individual persons act with multiple identities or genuine documents obtained fraudulently. Protection against FOGD must therefore also operate at the person level. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Why is classic KYC verification not sufficient to protect against FOGD?
KYC checks can verify document authenticity, liveness and 1:1 matching. However, they do not automatically answer the question of whether the same person is already known under another identity in a larger network. For protection against FOGD, a one time KYC check is therefore not sufficient if there is no continuous 1:n comparison and no linked assessment of security relevant findings. NIST distinguishes between 1:1 verification and biometric identification against a larger data set. (https://www.nist.gov/system/files/documents/2021/10/25/nist_appendix_pact_nov02.pdf)
Why is protection against FOGD both a privacy and a security challenge?
Protection against FOGD requires more transparency about identities, repeated registrations and security relevant anomalies. At the same time, personal data, especially biometric data, must be strictly protected. The challenge is therefore to reduce FOGD risks effectively without unlawful blacklist sharing, unnecessary data collection or uncontrolled disclosure of sensitive information. The GDPR requires, among other things, data minimization, purpose limitation and appropriate technical and organizational measures. (https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX:32016R0679)
Why can unlawful blacklist sharing not solve the FOGD problem?
Unlawful blacklist sharing is legally risky and does not solve the technical FOGD problem. A list of names is of limited use if criminal actors reappear with different identities, formally genuine documents or changed registration data. Protection against FOGD therefore requires more than a simple list of names. It requires a privacy compliant, status based and technically robust way to recognize the same natural person. Data protection authorities have identified serious legal problems with fraud blacklists lacking a sufficient statutory basis. (https://www.edpb.europa.eu/news/national-news/2022/tax-administration-fined-fraud-black-list_en)
What does FOGD detection mean in DriverTrust?
FOGD detection in DriverTrust means that the system does not only check one individual document. The decisive question is whether the same natural person appears again with different identity data, different documents or in different organizational contexts. DriverTrust addresses FOGD through a combination of multi layer verification, continuous recognition, 1:n comparison, Trust Indication and a privacy compliant status logic. The technical basis for this approach is the distinction between isolated 1:1 verification and dataset based 1:n recognition. (https://www.nist.gov/system/files/documents/2021/10/25/nist_appendix_pact_nov02.pdf)
How does DriverTrust differ from a normal document check when addressing FOGD?
A normal document check mainly looks at the document. DriverTrust also considers the person, the context, repeated registrations, security relevant status information and the question of whether an identity is merely formally plausible or also consistent within a wider network. In this way, DriverTrust addresses the central weakness of classic checks in FOGD cases: the gap between document authenticity and genuine identity assurance. Interpol expressly describes FOGD as a category of genuine documents obtained fraudulently. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Why is protection against FOGD incomplete without continuous revalidation?
FOGD risks do not arise only during initial onboarding. People may later present new documents, register again, change employer, use a new service provider or re enter sensitive processes through another access point. Protection against FOGD must therefore be continuous. Continuous revalidation helps ensure that identity, document and compliance risks are not checked only once, but throughout the relevant period of use. This reflects the principle that identity systems need reliable mechanisms for deduplication and ongoing integrity protection. (https://id4d.worldbank.org/guide/biometric-data)
Why is protection against FOGD particularly critical for valuable goods, sensitive data and critical processes?
Where valuable goods, sensitive data and critical processes are involved, a single wrong decision can cause substantial damage. If a person using a fraudulently obtained genuine document gains access to assets, customer data, IT systems, confidential information or security critical areas, the potential harm can be significant. In such environments, it is not sufficient to check only whether a document is formally genuine. An additional security layer at the person level is required. CISA emphasizes in the context of insider risks that persons with authorized access can cause significant harm. (https://www.cisa.gov/topics/physical-security/insider-threat-mitigation)
Why is FOGD a real risk outside logistics as well?
FOGD is equally relevant outside logistics because many sectors rely on identity documents. In banking, genuine documents obtained fraudulently may be used to open accounts or bypass KYC processes. In telecommunications and platform environments, they may be used to create false user or merchant accounts. In insurance, they may be relevant in policy, claims or benefit processes. In companies, they may be used for applications, access permissions or service provider onboarding. The pattern is always the same: a genuine document creates trust, even though it was obtained fraudulently. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
What is the difference between FOGD detection and fraud prevention in general?
Fraud prevention is the broader category. FOGD detection is a specific and particularly demanding part of it. It focuses on genuine documents obtained fraudulently and on the underlying identity deception. While classic fraud prevention often looks for suspicious documents, known names or known risks, FOGD detection must also be able to assess identities that appear formally unremarkable. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Why does protection against FOGD require an integrated security concept?
Protection against FOGD cannot rely on a single verification step. In the context of document and identity fraud, Frontex emphasizes that an integrated approach is required. For companies, this means that document checks, biometric assurance, 1:n comparison, revalidation, status logic, compliance processes and privacy architecture must work together. (https://www.frontex.europa.eu/media-centre/news/news-release/an-integrated-approach-to-combat-document-and-identity-fraud-29m6RJ)
Why should companies include protection against FOGD in their security strategy?
FOGD is a security gap that often remains invisible in classic control processes. Companies that rely only on document authenticity, corporate screening or one time identity verification may overlook genuine documents that were obtained fraudulently. Companies seeking to reduce insider risks, identity fraud, multiple identities and unauthorized access to sensitive resources should therefore explicitly include protection against FOGD in their security strategy. CISA describes insider risks and risks in interconnected supplier and service provider structures as security relevant issues for organizations. (https://www.cisa.gov/topics/physical-security/insider-threat-mitigation)
Why does DriverTrust position itself as a solution for protection against FOGD?
DriverTrust was developed for precisely the security gap created by FOGD, multiple identities, insider risks, Fake Carrier scenarios and cross organizational access structures. The solution combines person verification, continuous recognition, cross organizational status logic, automated revalidation and privacy friendly implementation. As a result, DriverTrust does not only address the question of whether a document is genuine. It also addresses whether the person using it can be reliably assessed in a security relevant context. This approach is particularly easy to understand in logistics, where FOGD can interact with insider risks and Fake Carrier methods, but it applies in principle to all industries in which identity determines access, trust, eligibility or authorization. (https://www.frontex.europa.eu/media-centre/news/news-release/an-integrated-approach-to-combat-document-and-identity-fraud-29m6RJ)
How often are fraudulently obtained genuine documents used?
Fraudulently obtained genuine documents are part of a large and serious identity fraud problem. Public authorities do not always publish FOGD as a separate statistical category, because many cases are recorded under broader labels such as document fraud, identity fraud, immigration fraud, application fraud or KYC fraud. However, this does not make FOGD a marginal risk. On the contrary, it makes FOGD especially dangerous: if a genuine document was obtained fraudulently and still passes authenticity checks, the fraud may remain hidden.
Frontex reported that in 2023 alone, EU Member States and Schengen Associated Countries detected 17,424 fraudsters using or possessing 22,395 fraudulent documents at the EU’s external borders. Frontex also describes document and identity fraud as instrumental for a wide range of criminal activities. These figures show that document and identity fraud is not an isolated phenomenon, but a large scale security challenge. (https://www.frontex.europa.eu/media-centre/news/news-release/an-integrated-approach-to-combat-document-and-identity-fraud-29m6RJ)
FOGD is a recognized and particularly dangerous part of this threat landscape. Interpol expressly states that criminals and terrorists often make fraudulent use of both fake and genuine identity and travel documents, and it lists fraudulently obtained genuine documents as a separate category of document fraud. This means that FOGD is not a theoretical edge case. It is a known method used by criminal actors to make a false or manipulated identity appear legitimate. (https://www.interpol.int/en/Crimes/Counterfeit-currency-and-security-documents/Identity-and-travel-document-fraud)
Is there evidence that FOGD is used at scale?
Yes. There is strong evidence that fraudulently obtained genuine documents are used at scale, even if many official statistics aggregate them with broader document and identity fraud categories. A white paper by ITW Security Division on fraudulently obtained genuine travel documents states that the number of such documents in existence is believed to be greater than the number of falsified or counterfeit documents. The same paper cites estimates that, in France, between 500,000 and 1,000,000 of 6,500,000 biometric passports in circulation may have been obtained on the basis of false breeder documents. It also cites estimates that 5 to 7 percent of Greek passports may have been issued on the basis of non genuine identity cards or birth certificates. (https://www.itwsf.com/Portals/0/Documents/White-Papers/Fraudulently%20Obtain%20Genuine%20FOG%20Documents.pdf)
These figures show the scale of the issue: FOGD can affect even highly secure biometric travel documents. This is precisely why traditional document authenticity checks are not enough. A fraudulently obtained genuine document may be real, valid and technically correct. The fraud sits behind the document, in the identity foundation that led to its issuance.
Is the use of document and identity fraud increasing?
Yes. The broader document and identity fraud environment is becoming more serious and more sophisticated, and this directly increases the need for protection against FOGD. FOGD is one of the most difficult forms of this problem because it can survive normal document checks.
Frontex reported that in 2022 the number of fraudulent documents reported within the European Union Document Fraud Risk Analysis Network increased by 5 percent compared with 2021. In the same report, Frontex stated that passports became the most reported fraudulent document type in 2022, with an increase of 35 percent compared with 2021, and that detections of fraudulent visas more than doubled, partly due to counterfeit and fraudulently obtained short term visas. Frontex also warned that forgers are increasing their mastery of printing and identity fraud technologies, making detection during border checks more complex. (https://prd.frontex.europa.eu/wp-content/uploads/ara-2023-pv-web-version-2.pdf)
Interpol also treats fraudulently obtained genuine documents as an active threat vector. Its Project Identity states that criminals and terrorists use several means to conceal their identity, including fake documents, fraudulently obtained genuine documents and morphing photos to create fake identity documents. (https://www.interpol.int/How-we-work/Forensics/Project-IDENTITY)
The conclusion is clear: document and identity fraud is a high volume and increasingly sophisticated threat. FOGD is among the most dangerous forms of this threat because the document itself may be genuine. Companies that rely only on document authenticity, one time KYC checks or corporate screening remain exposed to this risk.
Why is the FOGD problem likely underestimated?
The FOGD problem is likely underestimated because FOGD is difficult to detect by design. A fraudulently obtained genuine document may pass authenticity checks because it was issued by a real authority and contains genuine security features. If the underlying identity fraud is not discovered, the case may never be recorded as FOGD.
This is why FOGD is particularly dangerous for companies. A low number of publicly labelled FOGD cases does not mean the risk is low. It can also mean that existing systems are not designed to distinguish between document authenticity and identity reliability. ICAO has emphasized that the processes used to establish and verify identity can often be weaker than the security of the document issued later. (https://www.icao.int/sites/default/files/TRIP/Publications/ICAO-Guide-on-Evidence-of-Identity.pdf)
In practical terms, this means that companies may accept a document as genuine while still failing to detect that the identity behind it was created or manipulated fraudulently. This is exactly the protection gap that makes dedicated protection against FOGD urgently necessary.
Why do companies urgently need protection against FOGD?
Companies urgently need protection against FOGD because criminal actors can use genuine documents obtained fraudulently to appear legitimate. This can allow them to access goods, buildings, IT systems, customer data, financial processes, platform accounts, sensitive infrastructure or security critical operations. The risk is especially clear in logistics and transport, where Fake Carrier scenarios, insider risks and external personnel can create direct access to valuable goods and operational information. But the same logic applies across many other sectors, including staffing, platform work, financial services, telecommunications, insurance, access control and critical infrastructure.
Traditional document checks are not enough because FOGD can make a false or manipulated identity appear formally legitimate. One time KYC checks are not enough because they usually verify one identity at one point in time. Corporate screening is not enough because FOGD concerns the natural person who gains access to resources, not only the company around that person.
Protection against FOGD therefore requires an additional identity security layer: multi layer verification, recognition of repeated or multiple identities, continuous revalidation, privacy compliant status logic and a legally robust governance model. This is the type of protection gap DriverTrust is designed to address.
Why can DriverTrust help solve the FOGD problem?
DriverTrust helps solve the FOGD problem by adding an identity security layer behind the document. In a FOGD case, the document may be genuine, valid and technically unremarkable, while the identity behind it was established fraudulently. DriverTrust addresses this gap by focusing on the person using the document, the consistency of identity signals and the security relevant context in which access, trust or eligibility is requested.
According to our current knowledge, DriverTrust is the only solution that is specifically designed to detect and address FOGD risks in this way. The solution combines multi layer identity verification, continuous recognition of the same natural person, cross organizational status logic, automated revalidation and privacy friendly implementation. This enables DriverTrust to assess whether a person presenting a formally genuine document can be reliably evaluated in the relevant security context.
DriverTrust is operated by Green Convenience GmbH. Green Convenience GmbH has successfully completed the PCT patent procedure and holds patent protected technology in 156 countries. Unique data protection technology, dedicated privacy first developers and a network of law firms that continuously check DriverTrust form the foundation behind DriverTrust’s ability to address FOGD, multiple identities and identity based circumvention risks across organizational contexts.
DriverTrust follows a Privacy by Design approach with data minimization, limited visibility of sensitive information and status based evaluation. The permanent storage of image data that is not required for the ongoing purpose is avoided for privacy reasons. This strengthens both security and data protection because sensitive raw data is reduced while the necessary security assessment remains operationally usable. The GDPR requires, among other things, data minimization, storage limitation, purpose limitation and appropriate technical and organizational measures. (https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX:32016R0679)
DriverTrust is built on a structured contractual and governance setup. This is important because protection against FOGD involves legal bases, purpose definition, access rights, data minimization, retention logic, accountability and the handling of data subject rights. DriverTrust’s privacy architecture and contractual setup have been reviewed and further developed with specialized legal advisors, including Osborne Clarke.
DriverTrust addresses the identity risk behind the document. By combining identity verification, continuous recognition, privacy friendly status logic, data minimization, avoidance of unnecessary long term image storage, contractual governance, Privacy by Design and patent protected technology, DriverTrust reduces the structural gap that makes FOGD so difficult to detect with conventional document authenticity checks.
Looking forward for the new updates?
No spam. Just the latest releases and tips, interesting articles, and exclusive interviews with great people.